Member-only story
Credential Stuffing Explained: What is it? How to detect? How to prevent it?
The billions of login credentials available on the dark web make it easy for cybercriminals to steal login credentials. It has been widely reported that automated access data — the plug-in attack that has found its way onto the internet — is hitting systems such as credit cards, bank accounts, and credit card numbers.
Credential Stuffing is a technique that involves an automatic injection attack to access online services with stolen credentials. In an attack on the login data, fraudsters use it to access consumer accounts to make fraudulent purchases, carry out phishing attacks and steal information and money.

This attack method is facilitated by a range of off-the-shelf tools which are easily available, making it unsophisticated and relatively straightforward.
Commonly used tools include Sentry MBA, Account Hitman, Vertex, and Apex. To launch an attack, an attacker simply needs their tool of choice, a configuration file for the website to be attacked, and a list of username/password combinations to test against the site. Log-in attempts are typically directed through one or more proxies to hide the source of the attack. The software is set up to automatically insert the credentials from the username/password list into the corresponding fields contained within the GET or POST requests.
To carry out a large-scale attack on the credentials, malicious hackers use bots that fake different IP addresses and can automatically enter multiple accounts in parallel.
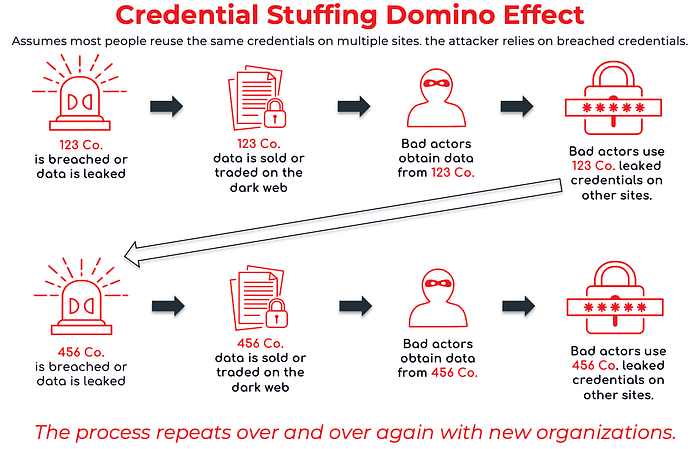
The credential stuffing uses known password-login-credentials combinations to make the process successful, not the references that make it successful. Such attacks take advantage of this behavior, relying on people to use matching passwords for multiple online accounts. While using the same username and password combinations on multiple websites increases the…
