Member-only story
Cybersecurity Maturity Model Certification (CMMC): Here is What You Need to Know!
The US Department of Defense has introduced the Cybersecurity Maturity Model Certification (CMMC) to normalize and standardize cybersecurity for the Federal Government and Defense Industrial Base (DIB). The CMMC is a unified standard that implements cybersecurity across the DIB, including over 300,000 companies in the supply chain. It is DoD’s response to a significant compromise of sensitive defense information contained in contractors’ information systems.
When the Department of Defense realized that under NIST SP 800–171 it needed more structure than self-certification and compliance it began to develop what would later become the Cybersecurity Maturity Model Certification (CMMC). Contractors are responsible for implementing, monitoring, and certifying the security of their information technology systems and the sensitive DOD information they store and transmit on these systems.
The Department of Defense (DoD) published version 1.0 of the proposed CMMC framework in January 2020. The new CMMC framework will serve as a verification mechanism to ensure that the appropriate levels of cybersecurity controls and processes are in place to protect Controlled Unclassified Information (CUI) located within the networks of ministries and industry partners. The CMMC report combines various cybersecurity standards and best practices and assigns them to different levels of maturity, from basic cyber hygiene to advanced ones. Given a CMMC level, these standards can be implemented to reduce the risk of certain cyber threats.
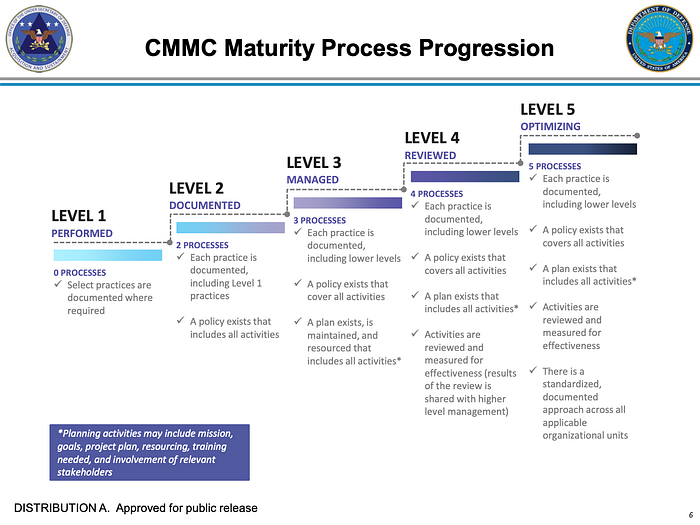
The five certification levels of CMMC reflect the maturity and reliability of an organization’s cybersecurity infrastructure that controls its ability to protect sensitive government information. The certification of the cybersecurity maturity model is based on an increasing level of preparation, with levels 1 (the lowest) to 5 (the most advanced). Each level defines processes, practices, objectives, and processes and practices…
