Member-only story
Trust And Federated Identity Management (FIM) vs Single Sign-On (SSO)
Any time an organization deploys a new app, end-users need to build a new set of credentials to recall. The outcome for staff? Too many passwords to remember. In reality, the average user needs to recall at least ten passwords a day but s/he forgets up to three of them every month.

The evolving challenges in identity management, in particular those related to identity theft, fraud, and other forms of identity abuse, have led to a new approach to identity management, now known as Federative Identity Management (FIM). Federated Identity Management is a relatively new concept that is part of an ongoing trend in identity management, an automated approach to managing identities such as passports, driving licenses, social security numbers, birth certificates, etc. There are many examples where two identity systems — management systems — are linked and can work together on the basis of mutual trust, for example in a social network.
What is Single Sign-On?
As the name suggests, SSO is a feature that enables users to access several web applications at once, using just one set of credentials.
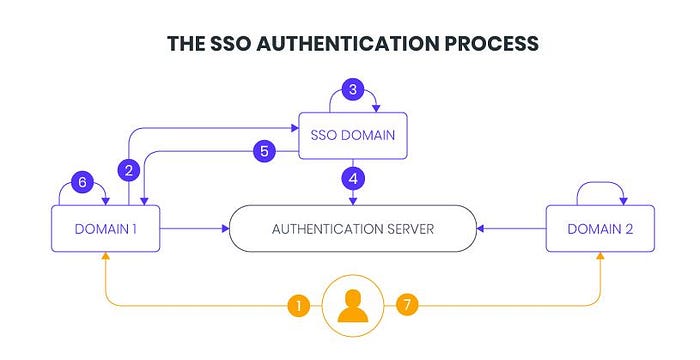
This allows people to do their job — because they don’t need to recall several credentials anymore — and also reduces the time that IT takes on password resets.
What is Federated Identity Management (FIM)?
A federated identity is linking a person’s electronic identity and attributes, stored across multiple distinct identity management systems.
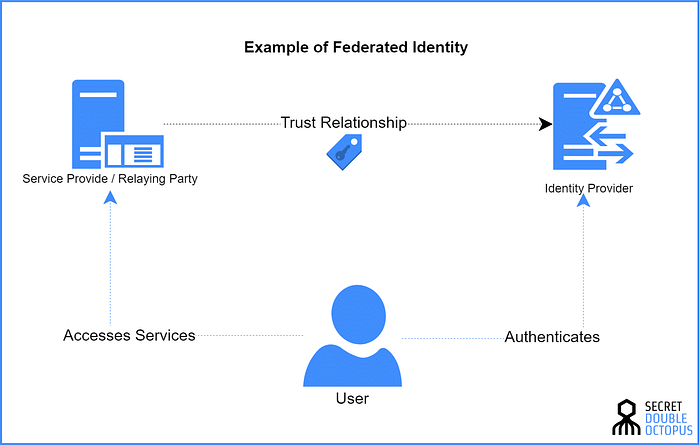
Federated identity is related to SSO, in which a user’s single authentication ticket, or token, is trusted across multiple IT systems or even organizations. SSO is a subset of…
